There is a meme going around right now that says to type in antifa.com and see what happens. Spoiler: antifa redirects to Joe Biden. That is antifa.com redirects to joebiden.com.
The political right says this shows Biden’s support for antifa. The political left is claiming it’s just some prankster pointing a domain to a server to make a presidential candidate look bad.
Let’s avoid the politics and break it down technically and see what’s going on.
Who Registered Antifa.com?
Antifa.com is registered at NameCheap. A quick search of their whois database at https://www.namecheap.com/domains/whois/result?domain=antifa.com reveals that the registrant opted for private registration in order to hide their identity. This is a perfectly legal, acceptable, and common practice as we explored in a previous blog post, but in this case, it does raise a question as to why the domain registration information would need to be private. A prankster would want to hide their identity else risk be exposed as not being part of the campaign, but with private registration there is at least doubt that the registrant could be part of the campaign.
Registrant Name: WhoisGuard Protected
Registrant Organization: WhoisGuard, Inc.
Registrant Street: P.O. Box 0823-03411
Registrant City: Panama
Registrant State/Province: Panama
Registrant Postal Code:
Registrant Country: PA
Registrant Email: [email protected]
Where are Antifa.com and joebiden.com hosted?
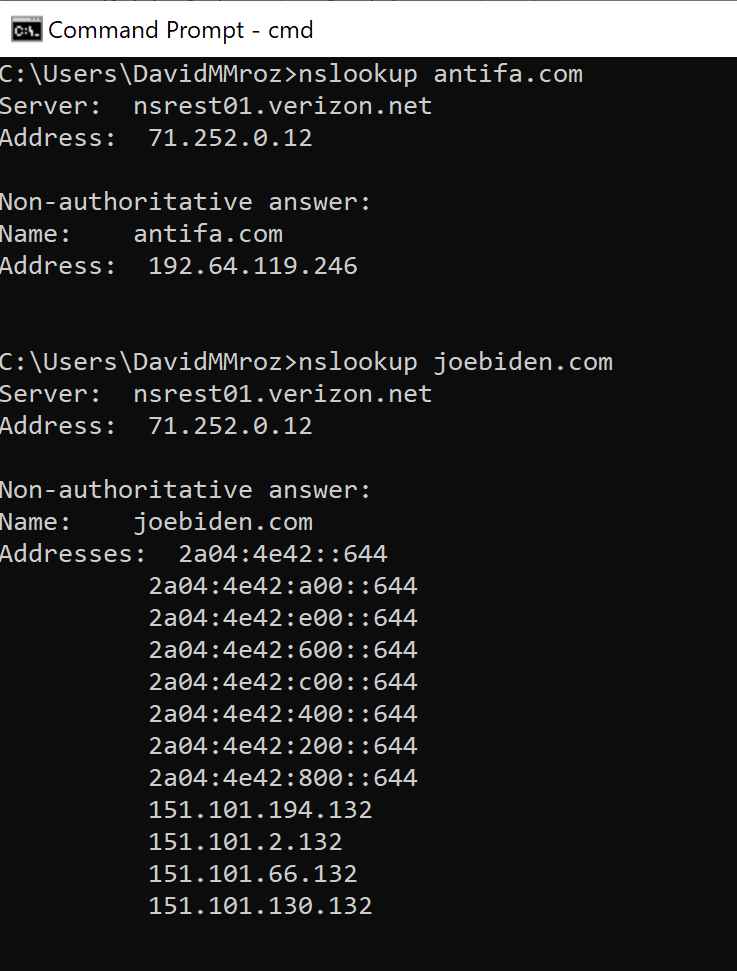
A quick lookup of joebiden.com shows that it is hosted at a server with the IP address of 151.101.130.132 that is owned by Fastly and antifa.com is hosted at a server with an IP address of 192.64.119.246 that is owned by NameCheap.
Now we know that joebiden.com and antifa.com are on different servers, so how does a user type in antifa.com and end up at joebiden.com? We originally did a deeper technical dive thinking this problem was more complex than it was, but the answer comes in a simple form of a simple redirect from antifa to joe biden.
If you are interested in in the test where we tried to force joebiden.com to answer requests for antifa.com, please read Does JoeBiden.com Host Antifa.com and then come back to this article for more information on what’s actually happening when antifa redirects to joe biden.
The Redirect from antifa.com to JoeBiden.com
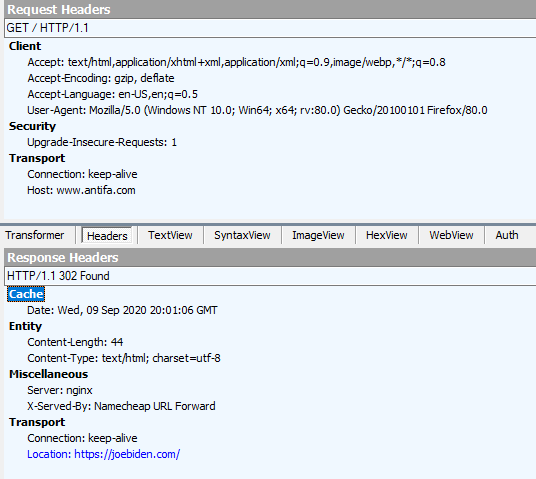
When a user types in antifa.com, their computer resolves the domain name to be the 192.64.119.246 address. That server at NameCheap responds with a header instructing the client (browser) to redirect to joebiden.com using an HTTP 302 (permanent) redirect. The client (browser) then resolves joebiden.com to be the server at 151.101.130.132 and the Fastly server serves up the joebiden.com website.
It is important to note that the Fastly server hosting joebiden.com is never asked to serve any files for antifa.com. From a technical perspective, they are two separate unrelated HTTP requests. After the client requests antifa.com and the NameCheap server returns the document with the redirect, the first transaction is complete. The client then kicks off a new request for joebiden.com to the Fastly server. Even though the user sees this as one fluid operation, it’s really two separate transactions with two separate DNS lookups, two separate HTML document requests on two separate domains on two separate servers. (It’s actually many more HTTP requests to fully load joebiden.com, but that’s outside of the scope of this post.)
Side note: As I was editing this post to confirm all of the details, I noticed that the chain of redirects had changed during the time it took me to write the first and second drafts. The original chain was antifa.com redirecting to kamalaharris.com which redirected to joebiden.com. As of September 9th, 2020, antifa.com redirects directly to joebiden.com. This does not change the analysis or the outcome, but it does indicate that the owner of antifa.com has updated the forwarder at NameCheap for some reason.
Analysis
So what does all of this mean?
The owner for joebiden.com and antifa.com are the same person/organization: Unconfirmed; neither registrant has public information.
The owner of antifa.com is a prankster: Possibly.
JoeBiden.com accepts redirects from kamalaharris.com: Confirmed
Joebiden.com accepts redirects from antifa.com: Confirmed
This is a prank?
Possibly. Without knowing the identity of the registrant at NameCheap, it’s difficult to say.
- It could be a prankster seeing how much traction this gets and how far it’ll spread before fact checkers start removing it from social media.
- It could be a political activist sowing discord.
- It could be state-sponsored political interference.
- It could be the Biden campaign subtly associating with antifa while publicly distancing themselves and keeping plausible deniability.
All of these are possibilities. The political ideologies of the individual will dictate the weight that is given to each theory. Our goal was to analyze this from an apolitical technical perspective so we’re not going to guess which one of the above is the real answer.
Does the campaign know that antifa redirects to joe biden?
They should. The Biden campaign has a talented social media team and we have to assume that they’re aware of the meme. We can also tell that joebiden.com is using Mixpanel, Google Analytics, and a number of other tracking and analytics tools to track users behavior not only on joebiden.com but on other websites and social media platforms as well. These tools will tell you where traffic originated and they’d be able to see antifa.com as one of the sources for the traffic. Fastly is a reputable company that hosts major websites and this information regarding the redirect from antifa.com to joebiden.com would also show up in the server logs. (It may be outside of the scope of contract for Fastly to review these logs for this type of data, but the campaign would still have it available to them to review if needed.)
Earlier in this post I indicated that “It is important to note that the Fastly server hosting joebiden.com is never asked to serve any files for antifa.com.” This is true in that the browser never asks the Fastly server hosting joebiden.com for files associated with antifa.com (and, as we proved in the article titled “Does JoeBiden.com Host Antifa.com” it wouldn’t work anyway), but the HTTP referer header does indicate that the user was redirected from antifa.com to joebiden.com and this information will appear in both the analytics tools and server logs.
Could joebiden.com reject any traffic that was intended for antifa.com?
Sure. By looking at the HTTP referer header they would be able to tell that traffic originated from antifa.com and block it or redirect to a page explicitly supporting or denouncing antifa.

2 Comments
It’s hard to imagine that referring sites are not logged by what was joebiden.com and now as of Jan 20,2021 is the new antifa.com redirect: Whitehouse.gov. As a matter of fact considering how much attention to supposed threats to the President, it would be unheard of. You can be certain, the Whitehouse.gov site is monitored. And that all traffic redirects are known and monitored.
I for one am sure that Antifa funneled oversees campaign contributions using Antifa.com redirected traffic.
As of today, antifa.com redirects to buildbackbetter.gov which redirects to whitehouse.gov. We agree that inbound traffic to whitehouse.gov surely must be monitored, but with this extra redirect they may have to stop it at buildbackbetter.gov, but that’s far from an insurmountable task.